Pro Cursor Rules vs RedVeil
Side-by-side comparison to help you choose the right AI tool.
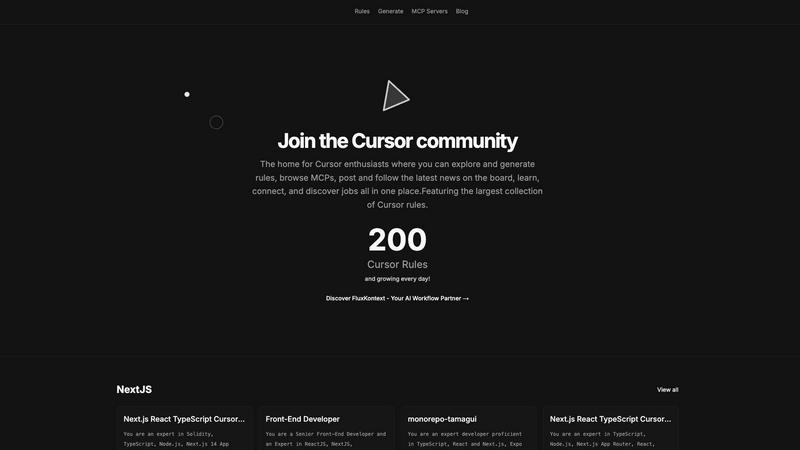
Pro Cursor Rules
Pro Cursor Rules connects Cursor enthusiasts to explore, create, and share the largest collection of Cursor rules and.
Last updated: February 28, 2026
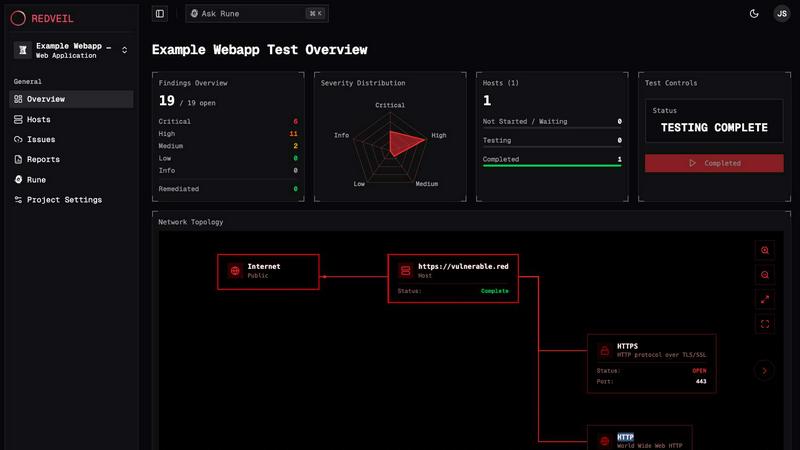
RedVeil
RedVeil delivers AI-driven penetration testing, uncovering vulnerabilities swiftly and cost-effectively for robust.
Last updated: February 28, 2026
Visual Comparison
Pro Cursor Rules
RedVeil
Feature Comparison
Pro Cursor Rules
Vast Collection of Cursor Rules
Pro Cursor Rules boasts the largest collection of Cursor rules available, a treasure trove for anyone looking to enhance their projects. Users can browse effortlessly through meticulously categorized rules that cater to various applications, ensuring they find exactly what they need to optimize their workflows.
Rule Generation Tool
The innovative rule generation tool allows users to create customized Cursor rules tailored to their specific needs. This feature streamlines the creative process, enabling designers and developers to generate rules that align perfectly with their unique projects, significantly enhancing productivity.
Community Engagement Hub
The platform fosters a thriving community atmosphere where users can connect, collaborate, and share insights. By providing discussion boards and networking opportunities, Pro Cursor Rules encourages users to engage with one another, facilitating a culture of support and knowledge sharing that enhances the overall user experience.
MCP Server Directory
Pro Cursor Rules includes an extensive directory of MCP servers, making it easier for users to discover and join communities that align with their interests. This feature not only broadens users' network of contacts but also enhances their ability to collaborate on exciting new projects with like-minded individuals.
RedVeil
AI-Powered Testing
RedVeil leverages intelligent AI agents that emulate the reasoning capabilities of human hackers. This allows for the identification of multi-step attack chains and the discovery of real, exploitable vulnerabilities within minutes, enhancing the efficiency of security assessments.
One-Click Reporting
Generate professional, audit-ready reports with just a single click. These reports are tailored for executives, engineers, and security teams, providing clear insights and actionable remediation steps, ensuring compliance with standards such as SOC 2, ISO 27001, and PCI-DSS.
On-Demand Testing
With RedVeil, users can initiate penetration tests whenever needed, without the delays associated with traditional scheduling. This flexibility allows teams to conduct assessments in real-time, especially after code deployments or changes in the environment.
Guided Remediation Support
RedVeil goes beyond just identifying vulnerabilities; it provides detailed remediation guidance. Users receive context-rich explanations of the findings, why they matter, and step-by-step instructions on how to mitigate the risks effectively, streamlining the remediation process.
Use Cases
Pro Cursor Rules
Enhancing Web Development Projects
Web developers can leverage Pro Cursor Rules to find and implement Cursor rules that enhance user interfaces and improve overall user experience. By utilizing the extensive library, developers can ensure their web applications are both functional and visually appealing.
Streamlining Design Processes
Designers can utilize the platform to generate custom Cursor rules that fit their specific creative needs. This tailored approach allows for a more fluid design process, enabling designers to produce unique and engaging visual elements that captivate users.
Community Collaboration and Networking
Users can engage with other Cursor enthusiasts to collaborate on projects, share ideas, and seek feedback. This community aspect fosters a rich exchange of knowledge and resources, allowing users to grow their skills and expand their professional networks.
Career Development Opportunities
Pro Cursor Rules serves as a resource for job seekers within the Cursor community. By connecting users with job opportunities and industry trends, the platform supports career advancement in the rapidly evolving tech landscape, making it a valuable tool for professional growth.
RedVeil
Continuous Integration/Continuous Deployment (CI/CD) Security
For organizations employing CI/CD practices, RedVeil enables rapid security assessments after each deployment. This ensures that vulnerabilities are detected and addressed in real-time, reducing the risk of security breaches in production environments.
Compliance Preparation
Companies needing to meet compliance standards can use RedVeil to conduct regular penetration tests and generate necessary documentation. This proactive approach simplifies the audit process and ensures that security measures align with regulatory requirements.
Agile Development Teams
Agile teams can benefit from RedVeil by integrating security testing into their sprints. With the ability to start tests on-demand, developers can receive immediate feedback on security issues, allowing them to incorporate fixes into their workflow seamlessly.
Risk Management
Organizations can utilize RedVeil to maintain an ongoing risk management strategy. By continuously testing their systems and receiving timely reports on vulnerabilities, teams can prioritize their security efforts based on real, exploitable risks rather than theoretical threats.
Overview
About Pro Cursor Rules
Pro Cursor Rules is an avant-garde platform meticulously crafted for Cursor enthusiasts, serving as a centralized hub where innovation meets creativity. This dynamic tool empowers developers, designers, and tech aficionados to explore, generate, and share an expansive array of Cursor rules that elevate productivity and artistic expression. With an extensive library brimming with diverse Cursor rules, users can effortlessly navigate through a plethora of options tailored to their unique needs. The platform not only facilitates rule generation but also immerses users in the latest news and trends from the Cursor community. By fostering a vibrant environment, Pro Cursor Rules encourages collaboration and connection among users, unveiling exciting job opportunities and resources that are invaluable for anyone engaged in the Cursor ecosystem. Ultimately, this platform revolutionizes workflows and creative projects, enabling users to harness Cursor technology to its fullest potential.
About RedVeil
RedVeil is a revolutionary AI-powered penetration testing platform designed to meet the fast-paced demands of modern software engineering. In an era where traditional pentesting methods can take weeks and cost thousands, RedVeil transforms the landscape by providing rapid, autonomous penetration tests that can be initiated in minutes. By combining the cognitive reasoning of human hackers with the speed and efficiency of cutting-edge software, RedVeil empowers teams to identify and remediate vulnerabilities quickly and effectively. This service is ideal for development teams, security professionals, and compliance officers who require continuous security assessments rather than static "point-in-time" evaluations. With RedVeil, organizations can confidently deploy code, knowing their security posture is examined in real-time, resulting in actionable, audit-ready reports delivered the same day.
Frequently Asked Questions
Pro Cursor Rules FAQ
What types of users benefit from Pro Cursor Rules?
Pro Cursor Rules is designed for a diverse audience, including developers, designers, and tech enthusiasts who are looking to enhance their productivity and creativity through the use of Cursor technology.
How do I generate my own Cursor rules?
Using the rule generation tool, users can easily create customized Cursor rules by inputting their desired specifications. This user-friendly feature streamlines the process, making it accessible for everyone.
Can I connect with other users on the platform?
Absolutely! Pro Cursor Rules has a community engagement hub that allows users to connect, collaborate, and share insights with fellow Cursor enthusiasts, fostering a supportive and interactive environment.
Is there a mobile application available for Pro Cursor Rules?
Currently, Pro Cursor Rules is primarily web-based. However, the platform is designed to be responsive and accessible on various devices, ensuring a seamless experience for users regardless of their device choice.
RedVeil FAQ
Does RedVeil perform a real penetration test?
Yes, RedVeil conducts genuine penetration tests using AI agents that simulate real attacker behavior, identifying actual vulnerabilities and providing actionable insights.
How many penetration tests can I do with my annual subscription?
The number of penetration tests you can conduct depends on your chosen subscription tier, which defines the number of Agent Ops allocated annually for testing.
Is there a chance that my web application or network could go down during the test?
RedVeil is designed to minimize impact. However, as with any penetration testing, there is always a slight risk. The platform provides guidance to help mitigate potential disruptions.
Can I use RedVeil's penetration test reports to meet the requirements of my compliance?
Absolutely. RedVeil generates compliance-ready reports that align with various standards such as SOC 2, ISO 27001, and PCI-DSS, making it easier for you to demonstrate your security posture to auditors.
Alternatives
Pro Cursor Rules Alternatives
Pro Cursor Rules is a cutting-edge platform tailored for Cursor enthusiasts, serving as a centralized hub for exploring, generating, and sharing Cursor rules. This innovative tool belongs to the AI Assistants category, catering to a diverse audience of developers, designers, and tech aficionados eager to amplify their productivity and creativity within the Cursor ecosystem. Users often seek alternatives to Pro Cursor Rules for various reasons, including pricing concerns, specific feature requirements, or compatibility with different platforms. When searching for an alternative, it is essential to consider factors such as the range of features offered, community engagement opportunities, and the overall user experience, ensuring that the selected option aligns with individual needs and aspirations.
RedVeil Alternatives
RedVeil is a revolutionary service in the realm of cybersecurity, offering on-demand penetration testing powered by advanced agentic AI technology. As organizations increasingly adopt agile development practices, the traditional approach to pentesting—characterized by lengthy timelines and high costs—often fails to meet the rapid pace of modern engineering. Users frequently seek alternatives to RedVeil due to factors such as pricing, the need for specific features, or compatibility with varying platforms and workflows. When searching for an alternative to RedVeil, it's essential to consider several key aspects. Look for solutions that offer a balance of speed and depth, ensuring comprehensive vulnerability assessment without compromising on quality. Additionally, prioritize flexibility in scheduling and reporting capabilities, as well as support for various compliance standards, to align with your organization's unique security needs and operational dynamics.
