iGPT vs Threat Watch
Side-by-side comparison to help you choose the right AI tool.
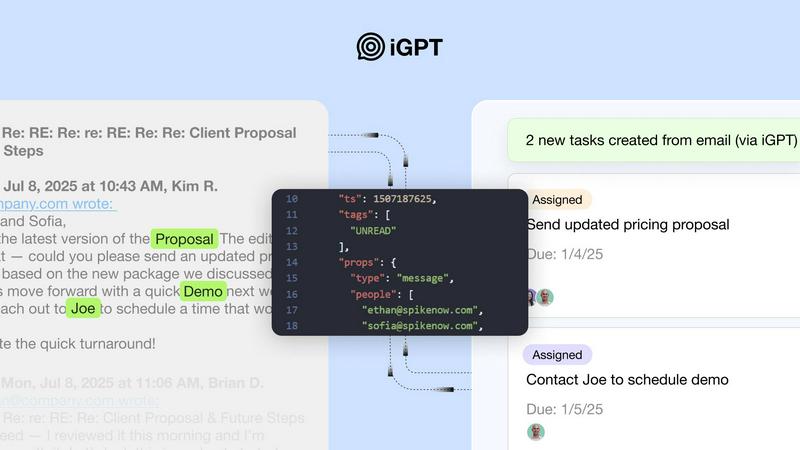
iGPT is the enterprise API that transforms messy email data into trusted, context-aware answers for AI agents.
Last updated: February 28, 2026
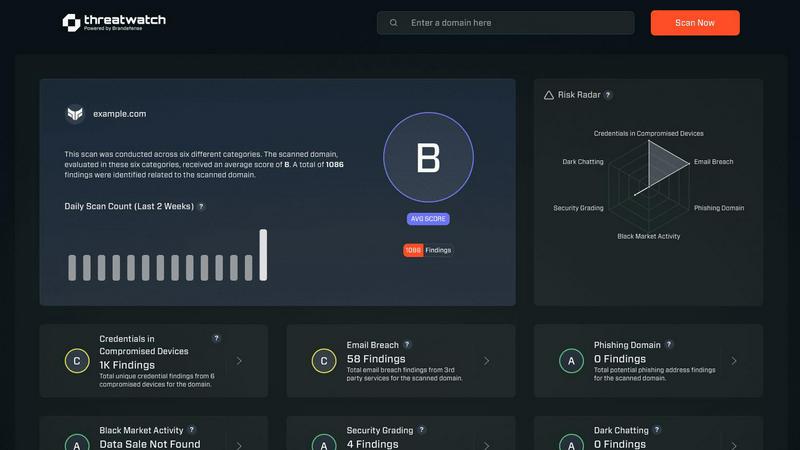
Threat Watch
Unleash AI-driven insights to swiftly identify and fortify your digital vulnerabilities for ultimate cybersecurity.
Last updated: February 28, 2026
Visual Comparison
iGPT
Threat Watch
Feature Comparison
iGPT
Unified Intelligence Endpoint
iGPT replaces entire multi-endpoint retrieval architectures with a single, powerful API call. Developers simply send a natural language query, and iGPT's integrated pipeline handles retrieval, sophisticated context shaping, and reasoning in one seamless operation. This eliminates the need to manage separate systems for parsing, vector stores, and prompt chains, dramatically accelerating development and reducing operational complexity for AI agents.
Autonomous Context Engineering
The platform autonomously handles the entire complex lifecycle of email intelligence. It performs real-time ingestion and deep indexing of messages and attachments, automatically reconstructs fragmented email threads across time and participants, and employs a hybrid retrieval system that combines semantic, keyword, and filter-based search. It then optimally shapes the context window for your LLM, delivering perfectly formatted, cited answers without any manual prompt tuning or maintenance.
Enterprise-Grade Security Fabric
iGPT is built with a zero-trust security architecture from the ground up. It enforces OAuth-only processing with strict Role-Based Access Control (RBAC) for every request and adheres to a rigorous zero-data-retention policy, where all inferences are processed in memory and never stored. Your data is never used to train models, ensuring full data sovereignty and providing a complete, immutable audit trail for all agentic actions.
Deep Attachment and Thread Intelligence
Beyond simple text, iGPT deeply processes all attachments—extracting text, data, and structure from documents, PDFs, and spreadsheets—and intelligently contextualizes this information within the email thread. It automatically rebuilds complete conversation threads, understanding relationships across time, participants, and attached files, turning disparate data points into a coherent, actionable narrative.
Threat Watch
Real-Time Threat Analysis
Threat Watch continuously monitors your digital environment, employing AI algorithms to analyze data in real-time. This ensures instant detection of anomalies and potential threats, allowing your team to respond swiftly and effectively.
Comprehensive Attack Surface Mapping
With Threat Watch, gain unparalleled visibility into your organization’s entire attack surface. It evaluates internal assets, software vulnerabilities, and external exposures, providing a holistic view of potential security gaps.
Autonomous Risk Prioritization
Leveraging advanced machine learning techniques, Threat Watch autonomously identifies and prioritizes risks based on their potential impact. This feature enables security teams to focus their efforts on the most pressing threats, streamlining incident response.
Predictive Cyber Health Insights
Threat Watch transforms historical data into predictive insights about your cyber health. By analyzing patterns and trends, it equips organizations with foresight, allowing them to anticipate attacks before they happen and enhance their security posture proactively.
Use Cases
iGPT
Autonomous Email Assistants
Build next-generation AI agents that can draft, prioritize, summarize, and act on email with full, cited context. These assistants understand nuanced requests, manage inboxes proactively, and execute follow-up actions based on the complete history of a conversation and its attachments, moving beyond simple drafting to true email orchestration.
Intelligent Workflow Automation
Transform unstructured email threads into structured, automated workflows. iGPT can automatically extract tasks, deadlines, approvals, and ownership details from conversations, flag stalled items, and feed this structured data into project management tools, CRMs, or ERP systems, turning communication into direct action.
Customer Support Copilots
Empower support teams with agents that instantly rebuild the entire customer story. By analyzing long, complex email chains, tone shifts, and all related attachments, iGPT provides support copilots with a complete historical context, enabling faster, more accurate resolutions and superior customer experiences.
Compliance and Audit Intelligence
Automate the tracing of feedback, approvals, decisions, and contractual rationale directly back to their source in original email conversations and attachments. iGPT creates a reliable, queryable audit trail, streamlining compliance processes, e-discovery, and internal reviews with agentic efficiency.
Threat Watch
Proactive Vulnerability Management
Organizations can utilize Threat Watch to conduct regular scans of their systems, identifying vulnerabilities before they are exploited by malicious actors. This proactive approach significantly reduces the risk of breaches.
Incident Response Optimization
In the event of a security incident, Threat Watch provides real-time insights that enhance incident response efforts. Security teams can leverage its analytics to understand the nature of the threat and respond with precision.
Dark Web Monitoring
Threat Watch actively scans the dark web for compromised credentials and sensitive information related to your organization. This invaluable feature allows you to take preventive measures before potential data breaches occur.
Compliance and Reporting
For organizations facing regulatory compliance challenges, Threat Watch simplifies the process by providing comprehensive reports on security health. This feature aids in demonstrating compliance with industry standards and regulations.
Overview
About iGPT
iGPT is the foundational intelligence layer for the agentic future, engineered to transform the world's most critical but chaotic communication medium—email—into structured, actionable, and trusted context. It is an enterprise-grade API that serves as a secure and auditable gateway, enabling AI agents and automated workflows to seamlessly access, comprehend, and leverage the vast intelligence trapped within sprawling email conversations and complex attachments. Built for developers and enterprises, iGPT surgically eliminates the traditional AI breakdown point: the immense complexity of parsing, chunking, indexing, and endless prompt-tuning required to make sense of messy, threaded, and document-rich email data. Its revolutionary core value proposition is a single, unified API call that delivers cited, context-aware answers in seconds, completely replacing fragile, multi-step retrieval pipelines. With end-to-end security, granular RBAC, and a strict zero-data-retention policy, iGPT empowers organizations to deploy autonomous agents with absolute confidence, ensuring compliance, maintaining data sovereignty, and unlocking unprecedented operational intelligence from the platform where real work actually happens.
About Threat Watch
Threat Watch transcends the conventional realm of cybersecurity tools, embodying a sentient intelligence layer that integrates seamlessly into your digital ecosystem. It represents a transformative leap in cyber defense, converting raw data into a dynamic, living assessment of your organization’s security posture. This platform acts as a centralized cyber health command center, continuously scrutinizing your entire attack surface. From internal assets and software vulnerabilities to external exposures across the clear, deep, and dark web, Threat Watch provides a comprehensive view of your security landscape. By harnessing advanced AI-driven analytics, it delivers real-time, predictive insights that elevate your security strategy from a reactive stance to a proactive and predictive posture. Designed for forward-thinking security teams, IT leaders, and executives, it offers more than mere alerts; it provides a clear, actionable, and prioritized roadmap to cyber resilience. The core strength of Threat Watch lies in its ability to autonomously identify, contextualize, and prioritize risks, empowering you to mitigate threats with unprecedented speed and surgical precision, effectively future-proofing your organization against the ever-evolving digital threat landscape.
Frequently Asked Questions
iGPT FAQ
How does iGPT differ from using a generic LLM API on email text?
While a generic LLM can process text, iGPT is a complete intelligence pipeline specifically engineered for email's unique chaos. It handles the entire stack: real-time ingestion, deep attachment parsing, automatic thread reconstruction, hybrid retrieval, and optimized context shaping—all through one API call. You avoid the months of engineering work required to parse, chunk, index, and prompt-tune a system capable of understanding real-world email data with citations.
What is the Context Engineering Framework (CEF)?
The Context Engineering Framework (CEF) is iGPT's proprietary, tiered system for optimizing the intelligence retrieval process. It allows developers to select different quality and speed profiles (like cef-1-normal) for their queries, balancing factors such as retrieval depth, reasoning complexity, and latency to match the specific needs of their agentic application, all without manual tuning.
How does iGPT ensure the security of my company's email data?
Security is foundational. iGPT employs OAuth-only authentication with granular Role-Based Access Control (RBAC), ensuring users and agents can only access data they are explicitly permitted to see. It operates on a strict zero-data-retention policy—all data is processed in memory for a single inference and is never stored or logged. Furthermore, your data is never used to train or improve any models.
Can iGPT connect to and index email data in real-time?
Yes. iGPT provides seamless integration methods to connect to your organization's email sources. Once connected, it performs continuous, real-time indexing, ensuring that the intelligence it provides is always based on the most up-to-date inbox state, attachments, and conversations, enabling agents to act on live information.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for a wide range of organizations, from small businesses to large enterprises. Any entity that seeks to enhance its cybersecurity posture can leverage this revolutionary tool to protect against evolving threats.
How does Threat Watch ensure data privacy?
Threat Watch adheres to strict data privacy standards and regulations. It employs encryption and data anonymization techniques to protect sensitive information while conducting its analyses, ensuring that your data remains secure.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is built to integrate seamlessly with a variety of existing security tools and systems. This interoperability enhances your current security infrastructure without disrupting workflows.
Is there support available for new users?
Absolutely. Threat Watch offers comprehensive support for new users, including onboarding assistance, tutorials, and a dedicated helpdesk to ensure that your team can maximize the benefits of the platform.
Alternatives
iGPT Alternatives
iGPT is an enterprise-grade API that serves as a foundational intelligence layer, transforming chaotic email data into structured, context-aware answers for AI agents. It belongs to the business intelligence category, specifically designed to solve the complex problem of making unstructured email communications actionable for autonomous systems. Users may explore alternatives for various reasons, including specific budget constraints, the need for different integration capabilities, or platform requirements that extend beyond email intelligence. The search often stems from a need to find the optimal fit for their unique technical stack and operational scale. When evaluating alternatives, prioritize solutions that offer robust, auditable security, genuine context-awareness beyond simple keyword search, and the ability to handle the inherent messiness of threaded conversations and attachments. The core value lies in eliminating multi-step data pipelines with a single, reliable API call that delivers trusted, cited intelligence.
Threat Watch Alternatives
Threat Watch is a cutting-edge cybersecurity platform that embodies the next generation of cyber defense through its AI-powered threat intelligence capabilities. As a vital component in the business intelligence category, it serves as a sentient intelligence layer that continuously analyzes and diagnoses your organization's security posture, transforming raw data into actionable insights. However, users often seek alternatives for various reasons, including pricing structures, desired features, or specific platform integrations that may better suit their unique needs. When exploring alternatives, it is essential to consider factors such as comprehensive analytics, real-time insights, the ability to prioritize risks, and overall ease of integration into existing systems. A robust alternative should not only offer a proactive approach to threat management but also ensure that the user experience is intuitive and aligns with your organization's specific cybersecurity objectives.
