Threat Watch
Unleash AI-driven insights to swiftly identify and fortify your digital vulnerabilities for ultimate cybersecurity.
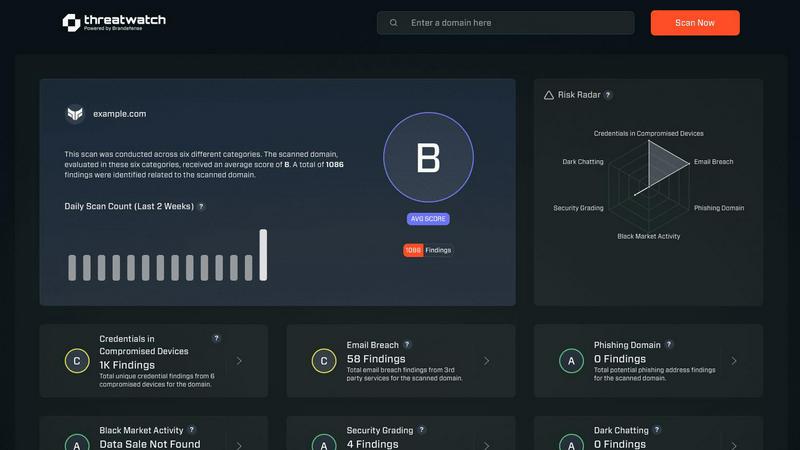
About Threat Watch
Threat Watch transcends the conventional realm of cybersecurity tools, embodying a sentient intelligence layer that integrates seamlessly into your digital ecosystem. It represents a transformative leap in cyber defense, converting raw data into a dynamic, living assessment of your organization’s security posture. This platform acts as a centralized cyber health command center, continuously scrutinizing your entire attack surface. From internal assets and software vulnerabilities to external exposures across the clear, deep, and dark web, Threat Watch provides a comprehensive view of your security landscape. By harnessing advanced AI-driven analytics, it delivers real-time, predictive insights that elevate your security strategy from a reactive stance to a proactive and predictive posture. Designed for forward-thinking security teams, IT leaders, and executives, it offers more than mere alerts; it provides a clear, actionable, and prioritized roadmap to cyber resilience. The core strength of Threat Watch lies in its ability to autonomously identify, contextualize, and prioritize risks, empowering you to mitigate threats with unprecedented speed and surgical precision, effectively future-proofing your organization against the ever-evolving digital threat landscape.
Features of Threat Watch
Real-Time Threat Analysis
Threat Watch continuously monitors your digital environment, employing AI algorithms to analyze data in real-time. This ensures instant detection of anomalies and potential threats, allowing your team to respond swiftly and effectively.
Comprehensive Attack Surface Mapping
With Threat Watch, gain unparalleled visibility into your organization’s entire attack surface. It evaluates internal assets, software vulnerabilities, and external exposures, providing a holistic view of potential security gaps.
Autonomous Risk Prioritization
Leveraging advanced machine learning techniques, Threat Watch autonomously identifies and prioritizes risks based on their potential impact. This feature enables security teams to focus their efforts on the most pressing threats, streamlining incident response.
Predictive Cyber Health Insights
Threat Watch transforms historical data into predictive insights about your cyber health. By analyzing patterns and trends, it equips organizations with foresight, allowing them to anticipate attacks before they happen and enhance their security posture proactively.
Use Cases of Threat Watch
Proactive Vulnerability Management
Organizations can utilize Threat Watch to conduct regular scans of their systems, identifying vulnerabilities before they are exploited by malicious actors. This proactive approach significantly reduces the risk of breaches.
Incident Response Optimization
In the event of a security incident, Threat Watch provides real-time insights that enhance incident response efforts. Security teams can leverage its analytics to understand the nature of the threat and respond with precision.
Dark Web Monitoring
Threat Watch actively scans the dark web for compromised credentials and sensitive information related to your organization. This invaluable feature allows you to take preventive measures before potential data breaches occur.
Compliance and Reporting
For organizations facing regulatory compliance challenges, Threat Watch simplifies the process by providing comprehensive reports on security health. This feature aids in demonstrating compliance with industry standards and regulations.
Frequently Asked Questions
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for a wide range of organizations, from small businesses to large enterprises. Any entity that seeks to enhance its cybersecurity posture can leverage this revolutionary tool to protect against evolving threats.
How does Threat Watch ensure data privacy?
Threat Watch adheres to strict data privacy standards and regulations. It employs encryption and data anonymization techniques to protect sensitive information while conducting its analyses, ensuring that your data remains secure.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is built to integrate seamlessly with a variety of existing security tools and systems. This interoperability enhances your current security infrastructure without disrupting workflows.
Is there support available for new users?
Absolutely. Threat Watch offers comprehensive support for new users, including onboarding assistance, tutorials, and a dedicated helpdesk to ensure that your team can maximize the benefits of the platform.
Explore more in this category:
Similar to Threat Watch
Decker
Decker is the deliverable OS that turns AI drafts into review-ready work and monetizes your expertise through proprietary training data.
AI Business Name Generator
Harness AI to instantly generate unique, brand-ready business names with available domains.
Opal44
Opal44 transforms your website traffic data into clear, actionable insights in plain English for smarter.
Fusedash
Fusedash transforms raw data into instant AI-powered dashboards for real-time team insights.
finban
finban empowers you to master liquidity planning for confident decisions on hiring, taxes, and investments without.
DeliveryNote.io
DeleteThreads is your autonomous AI agent for bulk Threads content deletion and digital footprint management.
aVenture
aVenture is an AI-powered platform for comprehensive startup research, competitor analysis, and investment tracking.
iGPT
iGPT is the enterprise API that transforms messy email data into trusted, context-aware answers for AI agents.
