Opal44 vs Threat Watch
Side-by-side comparison to help you choose the right AI tool.
Opal44 transforms your website traffic data into clear, actionable insights in plain English for smarter.
Last updated: March 4, 2026
Threat Watch
Unleash AI-driven insights to swiftly identify and fortify your digital vulnerabilities for ultimate cybersecurity.
Last updated: February 28, 2026
Visual Comparison
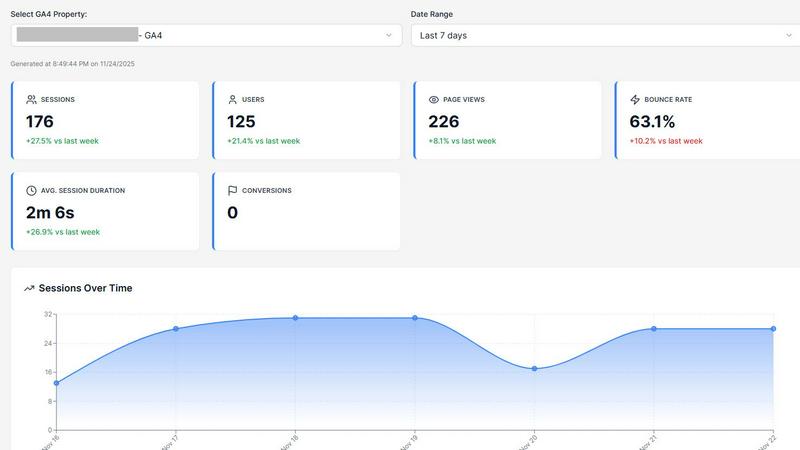
Opal44
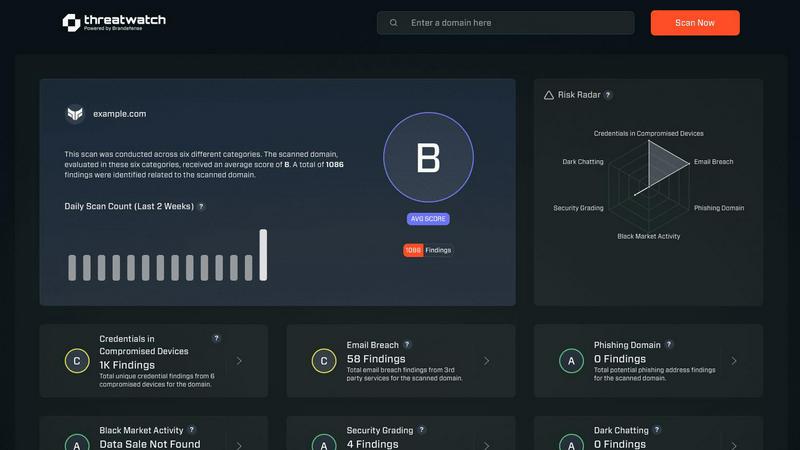
Threat Watch
Feature Comparison
Opal44
Plain English Insights
Opal44's standout feature is its ability to provide insights in simple, everyday language. By connecting directly to Google Analytics 4 data, it explains complex metrics, enabling users to grasp the underlying trends and patterns without needing a technical background.
Conversation-Style Reports
Gone are the days of deciphering convoluted reports. Opal44 delivers updates in a conversational style, making it feel like users are chatting with a personal analytics guide. This approach fosters a better understanding of data insights, making analytics more approachable for everyone.
Smart, Data-Driven Tips
Opal44 goes beyond simple reporting by offering tailored recommendations based on users' GA4 data. These insights help improve website traffic, boost conversions, and drive smarter business decisions, transforming raw data into strategic advantages.
Real-Time Alerts
Stay ahead of the curve with Opal44's real-time alert system. Users receive immediate notifications about significant changes in their traffic data, such as spikes or drops, allowing them to respond swiftly to unusual activity and optimize their strategies accordingly.
Threat Watch
Real-Time Threat Analysis
Threat Watch continuously monitors your digital environment, employing AI algorithms to analyze data in real-time. This ensures instant detection of anomalies and potential threats, allowing your team to respond swiftly and effectively.
Comprehensive Attack Surface Mapping
With Threat Watch, gain unparalleled visibility into your organization’s entire attack surface. It evaluates internal assets, software vulnerabilities, and external exposures, providing a holistic view of potential security gaps.
Autonomous Risk Prioritization
Leveraging advanced machine learning techniques, Threat Watch autonomously identifies and prioritizes risks based on their potential impact. This feature enables security teams to focus their efforts on the most pressing threats, streamlining incident response.
Predictive Cyber Health Insights
Threat Watch transforms historical data into predictive insights about your cyber health. By analyzing patterns and trends, it equips organizations with foresight, allowing them to anticipate attacks before they happen and enhance their security posture proactively.
Use Cases
Opal44
Small Business Growth
For small businesses, Opal44 simplifies the complex world of analytics, providing clear insights that help identify growth opportunities. By understanding which traffic sources drive the most engagement, owners can tailor their marketing efforts effectively.
E-commerce Optimization
E-commerce managers leverage Opal44 to enhance their online stores' performance. With actionable insights on customer behavior and conversion rates, they can implement strategies that lead to increased sales and customer retention.
Marketing Team Collaboration
Marketing teams can utilize Opal44 to ensure everyone is on the same page regarding website performance. The platform's easy-to-understand reports facilitate productive discussions, enabling teams to strategize effectively based on data-driven insights.
Client Reporting for Agencies
Digital agencies can use Opal44 to present clear, concise analytics reports to their clients. The platform's user-friendly format allows agencies to communicate complex data in a comprehensible manner, improving client relationships and satisfaction.
Threat Watch
Proactive Vulnerability Management
Organizations can utilize Threat Watch to conduct regular scans of their systems, identifying vulnerabilities before they are exploited by malicious actors. This proactive approach significantly reduces the risk of breaches.
Incident Response Optimization
In the event of a security incident, Threat Watch provides real-time insights that enhance incident response efforts. Security teams can leverage its analytics to understand the nature of the threat and respond with precision.
Dark Web Monitoring
Threat Watch actively scans the dark web for compromised credentials and sensitive information related to your organization. This invaluable feature allows you to take preventive measures before potential data breaches occur.
Compliance and Reporting
For organizations facing regulatory compliance challenges, Threat Watch simplifies the process by providing comprehensive reports on security health. This feature aids in demonstrating compliance with industry standards and regulations.
Overview
About Opal44
Opal44 is a revolutionary AI-driven analytics tool that transforms the way businesses interpret their website traffic data, specifically from Google Analytics 4. Designed for marketers, business owners, and anyone seeking actionable insights, Opal44 eliminates the confusion surrounding complex analytics dashboards. By translating intricate data sets into clear, actionable English, it empowers users to make informed decisions without the burden of jargon. The platform not only simplifies the analytics experience but also provides smart, data-driven tips tailored to enhance website performance. With a swift setup of just two minutes and a commitment to data security, Opal44 prioritizes user experience and empowers teams to harness their data's true potential, making it an invaluable asset for organizations of all sizes.
About Threat Watch
Threat Watch transcends the conventional realm of cybersecurity tools, embodying a sentient intelligence layer that integrates seamlessly into your digital ecosystem. It represents a transformative leap in cyber defense, converting raw data into a dynamic, living assessment of your organization’s security posture. This platform acts as a centralized cyber health command center, continuously scrutinizing your entire attack surface. From internal assets and software vulnerabilities to external exposures across the clear, deep, and dark web, Threat Watch provides a comprehensive view of your security landscape. By harnessing advanced AI-driven analytics, it delivers real-time, predictive insights that elevate your security strategy from a reactive stance to a proactive and predictive posture. Designed for forward-thinking security teams, IT leaders, and executives, it offers more than mere alerts; it provides a clear, actionable, and prioritized roadmap to cyber resilience. The core strength of Threat Watch lies in its ability to autonomously identify, contextualize, and prioritize risks, empowering you to mitigate threats with unprecedented speed and surgical precision, effectively future-proofing your organization against the ever-evolving digital threat landscape.
Frequently Asked Questions
Opal44 FAQ
How does Opal44 ensure data security?
Opal44 prioritizes user privacy by ensuring that all GA4 data remains secure. The platform does not sell or share user information, guaranteeing that your analytics data is solely yours.
What is the setup process like?
Setting up Opal44 is incredibly quick and straightforward. Users can securely connect their GA4 account in just two minutes, allowing them to start receiving insights almost immediately.
Can I try Opal44 for free?
Yes! New users can start a 7-day free trial with 50 actions, allowing them to explore the platform's full range of features without any financial commitment.
What types of businesses can benefit from Opal44?
Opal44 is designed for a wide range of businesses, from small startups to large agencies. Its user-friendly interface and plain English insights make it accessible for anyone looking to improve their understanding of website analytics.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for a wide range of organizations, from small businesses to large enterprises. Any entity that seeks to enhance its cybersecurity posture can leverage this revolutionary tool to protect against evolving threats.
How does Threat Watch ensure data privacy?
Threat Watch adheres to strict data privacy standards and regulations. It employs encryption and data anonymization techniques to protect sensitive information while conducting its analyses, ensuring that your data remains secure.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is built to integrate seamlessly with a variety of existing security tools and systems. This interoperability enhances your current security infrastructure without disrupting workflows.
Is there support available for new users?
Absolutely. Threat Watch offers comprehensive support for new users, including onboarding assistance, tutorials, and a dedicated helpdesk to ensure that your team can maximize the benefits of the platform.
Alternatives
Opal44 Alternatives
Opal44 is a groundbreaking tool that belongs to the Business Intelligence category, harnessing the power of AI to provide users with simple, actionable insights about their website traffic derived from Google Analytics 4. Its revolutionary approach eliminates jargon, allowing users to obtain valuable information through straightforward questions, making data accessibility easier than ever. However, users often seek alternatives to Opal44 due to various factors such as pricing, specific feature sets, or compatibility with different platforms. When searching for a suitable alternative, it's essential to evaluate aspects such as ease of use, the depth of insights provided, integration capabilities, and overall value to ensure that the chosen solution aligns with your unique business needs and objectives.
Threat Watch Alternatives
Threat Watch is a cutting-edge cybersecurity platform that embodies the next generation of cyber defense through its AI-powered threat intelligence capabilities. As a vital component in the business intelligence category, it serves as a sentient intelligence layer that continuously analyzes and diagnoses your organization's security posture, transforming raw data into actionable insights. However, users often seek alternatives for various reasons, including pricing structures, desired features, or specific platform integrations that may better suit their unique needs. When exploring alternatives, it is essential to consider factors such as comprehensive analytics, real-time insights, the ability to prioritize risks, and overall ease of integration into existing systems. A robust alternative should not only offer a proactive approach to threat management but also ensure that the user experience is intuitive and aligns with your organization's specific cybersecurity objectives.
