Pursuit vs Threat Watch
Side-by-side comparison to help you choose the right AI tool.
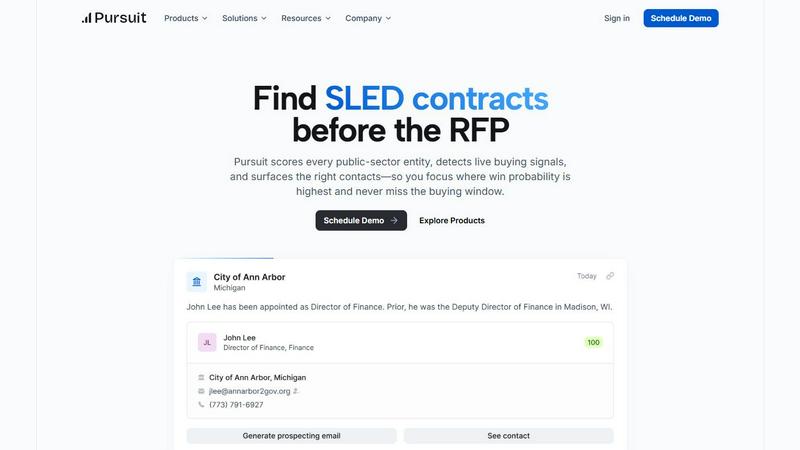
Pursuit
Pursuit's AI surfaces hidden SLED opportunities years before RFPs exist.
Last updated: February 28, 2026
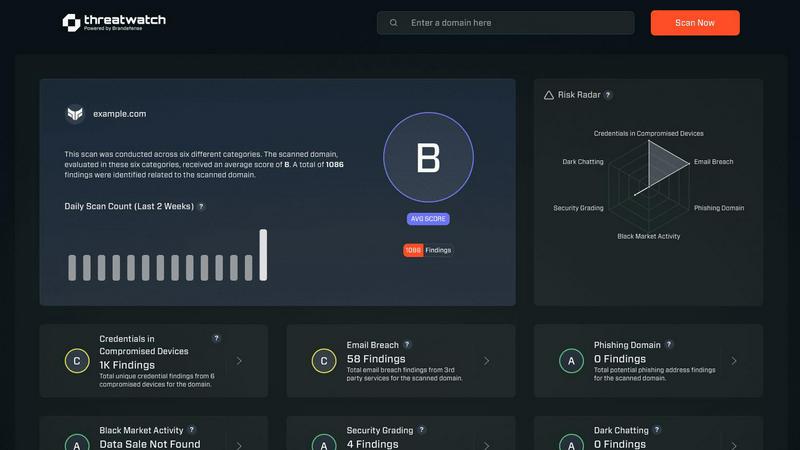
Threat Watch
Unleash AI-driven insights to swiftly identify and fortify your digital vulnerabilities for ultimate cybersecurity.
Last updated: February 28, 2026
Visual Comparison
Pursuit
Threat Watch
Feature Comparison
Pursuit
Pre-RFP Signal Intelligence Engine
At the core of Pursuit is a proprietary AI engine that continuously scans and analyzes millions of data points across 110,000+ SLED entities. It identifies and scores genuine buying signals—such as budget approvals, new strategic initiatives, leadership changes, and expiring contracts—6 to 18 months before an RFP is released. This transforms your team's approach from chasing public notices to shaping opportunities from their inception, ensuring you are the first and most prepared vendor in the room.
Entity Scoring & Prioritization
Pursuit eliminates guesswork by dynamically scoring every public-sector entity based on live buying signals, budget alignment, and historical procurement patterns. This provides an actionable, ranked list of accounts where the probability of winning is maximized. Sales and marketing teams can instantly focus their efforts on high-intent targets, moving beyond static territory maps to dynamic, signal-driven prioritization that adapts in real-time.
Native CRM & Stack Integrations
Pursuit is built for seamless operation within your existing tech ecosystem. It offers bi-directional, native synchronization with major CRMs like Salesforce and HubSpot, ensuring enriched account data, contact details, org charts, and live signals flow automatically into your team's workflow. This eliminates manual data entry, reduces enrichment time by over two-thirds, and creates a single source of truth across marketing, sales, and customer success.
Role-Specific Intelligence Delivery
Intelligence is delivered in the context of each user's role. Account Executives get instant meeting prep via a Chrome extension. BDRs receive daily, prioritized call lists. Marketing ops builds audiences from real budget cycles. Customer Success monitors for renewal and churn signals. This ensures every team member acts on the most relevant insights without sifting through irrelevant data, driving efficiency and impact at every stage of the customer lifecycle.
Threat Watch
Real-Time Threat Analysis
Threat Watch continuously monitors your digital environment, employing AI algorithms to analyze data in real-time. This ensures instant detection of anomalies and potential threats, allowing your team to respond swiftly and effectively.
Comprehensive Attack Surface Mapping
With Threat Watch, gain unparalleled visibility into your organization’s entire attack surface. It evaluates internal assets, software vulnerabilities, and external exposures, providing a holistic view of potential security gaps.
Autonomous Risk Prioritization
Leveraging advanced machine learning techniques, Threat Watch autonomously identifies and prioritizes risks based on their potential impact. This feature enables security teams to focus their efforts on the most pressing threats, streamlining incident response.
Predictive Cyber Health Insights
Threat Watch transforms historical data into predictive insights about your cyber health. By analyzing patterns and trends, it equips organizations with foresight, allowing them to anticipate attacks before they happen and enhance their security posture proactively.
Use Cases
Pursuit
Proactive Pipeline Generation for Sales Leaders
Sales leaders leverage Pursuit to build a predictable, high-quality pipeline without increasing headcount. By having full visibility into team-wide signal activity and territory coverage, they can strategically allocate resources, forecast based on real buying indicators, and coach reps on high-probability opportunities. This data-driven command center has been proven to increase pipeline by 6.6x, transforming sales leadership from management to strategic foresight.
Signal-Driven ABM Campaigns for Marketing
Marketing teams transition from broad awareness to precise, signal-driven Account-Based Marketing. Pursuit allows them to build hyper-targeted campaigns around concrete events like budget approvals or contract expirations. These qualified audiences can be synced directly to platforms like LinkedIn Ads, Marketo, or HubSpot, resulting in campaign conversion lifts of 2.4x by engaging accounts when they are actively planning purchases.
Prioritized Outreach for Business Development Reps (BDRs)
BDRs stop cold calling blindly and start engaging with purpose. Pursuit provides daily alerts and curated contact lists based on live buying signals specific to their territory, such as a new technology initiative or a key leadership change. This context allows for highly relevant, one-click outreach, dramatically improving connection rates and contributing to a 47% increase in qualified pipeline generation.
Early Renewal & Risk Identification for Customer Success
Customer Success teams shift from reactive renewal conversations to proactive relationship management. Pursuit configures alerts 90-180 days before contract renewals and monitors accounts for churn risk signals like budget cuts or competitor engagement. This early-warning system allows CSMs to intervene strategically, secure expansions, and mitigate attrition, identifying renewal opportunities 3x faster.
Threat Watch
Proactive Vulnerability Management
Organizations can utilize Threat Watch to conduct regular scans of their systems, identifying vulnerabilities before they are exploited by malicious actors. This proactive approach significantly reduces the risk of breaches.
Incident Response Optimization
In the event of a security incident, Threat Watch provides real-time insights that enhance incident response efforts. Security teams can leverage its analytics to understand the nature of the threat and respond with precision.
Dark Web Monitoring
Threat Watch actively scans the dark web for compromised credentials and sensitive information related to your organization. This invaluable feature allows you to take preventive measures before potential data breaches occur.
Compliance and Reporting
For organizations facing regulatory compliance challenges, Threat Watch simplifies the process by providing comprehensive reports on security health. This feature aids in demonstrating compliance with industry standards and regulations.
Overview
About Pursuit
Pursuit is the pre-RFP intelligence platform that is fundamentally rewriting the rules of engagement for public sector sales. It is a cutting-edge, AI-native operating system designed to give government contractors and their go-to-market teams a decisive, data-driven advantage. The platform transcends traditional sales intelligence by focusing on the critical 6-18 month window before a formal Request for Proposal (RFP) is ever published. By deploying advanced algorithms to continuously monitor and score over 110,000 SLED (State, Local, and Education) entities, Pursuit surfaces live buying signals—buried in budget documents, council meetings, and contract expirations—that competitors miss. This paradigm shift moves teams from reactive bidding to proactive strategy, allowing them to identify, engage, and position themselves as the incumbent solution long before the official procurement cycle begins. The result is a radical transformation of the sales pipeline: qualified opportunities multiply, win rates soar, and revenue operations run with unprecedented precision and foresight.
About Threat Watch
Threat Watch transcends the conventional realm of cybersecurity tools, embodying a sentient intelligence layer that integrates seamlessly into your digital ecosystem. It represents a transformative leap in cyber defense, converting raw data into a dynamic, living assessment of your organization’s security posture. This platform acts as a centralized cyber health command center, continuously scrutinizing your entire attack surface. From internal assets and software vulnerabilities to external exposures across the clear, deep, and dark web, Threat Watch provides a comprehensive view of your security landscape. By harnessing advanced AI-driven analytics, it delivers real-time, predictive insights that elevate your security strategy from a reactive stance to a proactive and predictive posture. Designed for forward-thinking security teams, IT leaders, and executives, it offers more than mere alerts; it provides a clear, actionable, and prioritized roadmap to cyber resilience. The core strength of Threat Watch lies in its ability to autonomously identify, contextualize, and prioritize risks, empowering you to mitigate threats with unprecedented speed and surgical precision, effectively future-proofing your organization against the ever-evolving digital threat landscape.
Frequently Asked Questions
Pursuit FAQ
How does Pursuit find buying signals before an RFP?
Pursuit's AI engine is specifically trained to parse the unstructured data of the public sector. It continuously monitors sources like government budget documents, meeting minutes, strategic plans, contract registries, and procurement portals. By analyzing language, timelines, and fiscal patterns, it identifies early-stage project planning, budget allocations, and problem statements that precede a formal RFP by 6-18 months, surfacing the intent long before the bid is public.
What makes Pursuit different from other sales intelligence tools?
Traditional sales intelligence tools are built for the commercial sector and often provide backward-looking firmographic data. Pursuit is purpose-built for the unique, complex SLED landscape. Its differentiation lies in its exclusive focus on pre-RFP signals, its entity-scoring algorithm tailored to public procurement cycles, and its role-specific workflows that deliver actionable intelligence—not just data—directly into the tools each team member uses daily.
How accurate and current is the data in Pursuit?
Pursuit maintains a 94% data accuracy rate through continuous, automated enrichment. The platform's systems are designed for real-time monitoring, meaning that new buying signals, contact changes, and organizational updates are captured and integrated as they happen. This ensures teams are always operating on the most current intelligence, not outdated snapshots.
Can Pursuit integrate with our existing CRM and marketing stack?
Absolutely. Pursuit is built with seamless integration as a core principle. It offers native, bi-directional sync with leading CRMs like Salesforce and HubSpot, requiring no engineering resources to set up. It also integrates with marketing automation platforms (e.g., Marketo) and advertising channels (e.g., LinkedIn) to push audience segments directly, ensuring intelligence flows automatically into your entire go-to-market stack.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for a wide range of organizations, from small businesses to large enterprises. Any entity that seeks to enhance its cybersecurity posture can leverage this revolutionary tool to protect against evolving threats.
How does Threat Watch ensure data privacy?
Threat Watch adheres to strict data privacy standards and regulations. It employs encryption and data anonymization techniques to protect sensitive information while conducting its analyses, ensuring that your data remains secure.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is built to integrate seamlessly with a variety of existing security tools and systems. This interoperability enhances your current security infrastructure without disrupting workflows.
Is there support available for new users?
Absolutely. Threat Watch offers comprehensive support for new users, including onboarding assistance, tutorials, and a dedicated helpdesk to ensure that your team can maximize the benefits of the platform.
Alternatives
Pursuit Alternatives
Pursuit is a next-generation business intelligence platform, engineered to decode the public sector. It leverages predictive AI to identify live buying signals and score opportunities, transforming how sales teams and government contractors engage with this complex market. This approach maximizes revenue by focusing efforts where the probability of winning is highest. Users explore alternatives for various reasons, including budget constraints, specific feature requirements, or the need for a different platform integration. The search often stems from a desire to compare core capabilities like data accuracy, alert systems, and the depth of AI-driven insights against other solutions in the space. When evaluating an alternative, prioritize platforms with robust, real-time data streams and genuine predictive analytics. The ideal solution should not only surface opportunities but also provide actionable intelligence, seamlessly integrate into your workflow, and demonstrably shorten the sales cycle within the public sector arena.
Threat Watch Alternatives
Threat Watch is a cutting-edge cybersecurity platform that embodies the next generation of cyber defense through its AI-powered threat intelligence capabilities. As a vital component in the business intelligence category, it serves as a sentient intelligence layer that continuously analyzes and diagnoses your organization's security posture, transforming raw data into actionable insights. However, users often seek alternatives for various reasons, including pricing structures, desired features, or specific platform integrations that may better suit their unique needs. When exploring alternatives, it is essential to consider factors such as comprehensive analytics, real-time insights, the ability to prioritize risks, and overall ease of integration into existing systems. A robust alternative should not only offer a proactive approach to threat management but also ensure that the user experience is intuitive and aligns with your organization's specific cybersecurity objectives.
