Deeploy vs Threat Watch
Side-by-side comparison to help you choose the right AI tool.
Deeploy
Deeploy governs and scales your AI with complete oversight and control.
Last updated: February 28, 2026
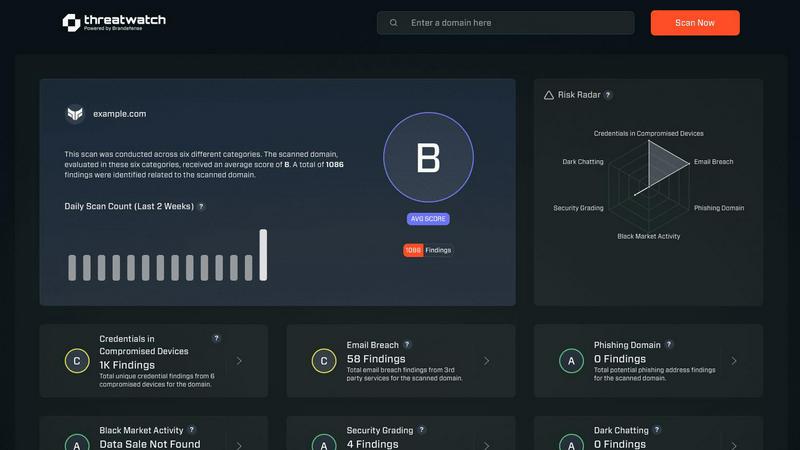
Threat Watch
Unleash AI-driven insights to swiftly identify and fortify your digital vulnerabilities for ultimate cybersecurity.
Last updated: February 28, 2026
Visual Comparison
Deeploy
Threat Watch
Feature Comparison
Deeploy
AI Discovery and Onboarding
Deeploy provides complete visibility across your entire AI landscape, eliminating dangerous blind spots. It allows you to discover, onboard, and manage every AI system in your organization from a single, unified interface. The platform connects seamlessly to any MLOps or GenAI platform, enabling centralized control and oversight without the need for costly and disruptive migration projects. This foundational feature creates a living, centralized inventory, turning AI chaos into a mapped and manageable portfolio.
Control Frameworks
Navigate the complex web of AI regulations with confidence using Deeploy's guided control frameworks. The platform offers default frameworks aligned with major standards like ISO 42001 and the NIST AI RMF, or allows you to build custom ones tailored to your specific needs. This system enables you to classify AI system risk levels in minutes and establish clear accountability with structured approval processes. It transforms abstract compliance requirements into straightforward, executable workflows.
Control Implementation
Deeploy turns governance frameworks into enforceable, engineer-friendly controls. It automatically assigns the right requirements to every AI system without manual intervention, giving technical teams clear and actionable tasks. The platform accelerates compliance by up to 90% through the use of intelligent templates and automated evidence collection. It even leverages AI-powered assessments to handle repetitive governance work, ensuring policies are actually followed and implemented.
Real-Time Monitoring and Explainability
Prevent AI incidents before they happen with Deeploy's predictive monitoring suite. The system provides instant alerts for critical issues like model drift, performance degradation, or output anomalies, often identifying problems before end-users are impacted. It adds essential tracing and guardrails to protect LLM outputs and ensures full auditability. Combined with built-in explainability features, it provides transparency into model decisions, building trust and enabling continuous improvement.
Threat Watch
Real-Time Threat Analysis
Threat Watch continuously monitors your digital environment, employing AI algorithms to analyze data in real-time. This ensures instant detection of anomalies and potential threats, allowing your team to respond swiftly and effectively.
Comprehensive Attack Surface Mapping
With Threat Watch, gain unparalleled visibility into your organization’s entire attack surface. It evaluates internal assets, software vulnerabilities, and external exposures, providing a holistic view of potential security gaps.
Autonomous Risk Prioritization
Leveraging advanced machine learning techniques, Threat Watch autonomously identifies and prioritizes risks based on their potential impact. This feature enables security teams to focus their efforts on the most pressing threats, streamlining incident response.
Predictive Cyber Health Insights
Threat Watch transforms historical data into predictive insights about your cyber health. By analyzing patterns and trends, it equips organizations with foresight, allowing them to anticipate attacks before they happen and enhance their security posture proactively.
Use Cases
Deeploy
Enterprise-Wide AI Governance and Compliance
Large organizations deploying AI across multiple departments use Deeploy to establish a single source of truth for all AI assets. This central command center enables Chief AI Officers and compliance teams to maintain an inventory, enforce standardized risk assessment protocols, and automatically generate the documentation needed to prove adherence to regulations like the EU AI Act, transforming a manual, high-risk process into an automated, reliable system.
Scaling MLOps with Guardrails
AI and data science teams leverage Deeploy to scale their model deployment velocity safely. The platform integrates into existing MLOps pipelines, providing the essential governance layer that ensures every deployed model meets organizational standards for fairness, performance, and security. It reduces deployment time from weeks to hours while providing the observability and explainability needed for both technical and non-technical stakeholders.
Governing Generative AI Applications
Companies building customer-facing applications with large language models (LLMs) use Deeploy to implement critical guardrails. The platform monitors LLM outputs in real-time for hallucinations, toxicity, or data leakage, triggering alerts and interventions. It provides the tracing and audit trails necessary to understand why an AI made a specific decision, which is crucial for high-stakes industries like healthcare, finance, and legal services.
Managing Vendor and Embedded AI Risk
For businesses utilizing third-party AI APIs or embedded AI within purchased software, Deeploy acts as a risk management hub. It allows organizations to discover and onboard these external AI systems into their governance framework, assessing their risk classification and ensuring they are monitored for performance and compliance. This eliminates a major blind spot in modern enterprise AI strategy.
Threat Watch
Proactive Vulnerability Management
Organizations can utilize Threat Watch to conduct regular scans of their systems, identifying vulnerabilities before they are exploited by malicious actors. This proactive approach significantly reduces the risk of breaches.
Incident Response Optimization
In the event of a security incident, Threat Watch provides real-time insights that enhance incident response efforts. Security teams can leverage its analytics to understand the nature of the threat and respond with precision.
Dark Web Monitoring
Threat Watch actively scans the dark web for compromised credentials and sensitive information related to your organization. This invaluable feature allows you to take preventive measures before potential data breaches occur.
Compliance and Reporting
For organizations facing regulatory compliance challenges, Threat Watch simplifies the process by providing comprehensive reports on security health. This feature aids in demonstrating compliance with industry standards and regulations.
Overview
About Deeploy
Deeploy is the foundational command center for the AI-native enterprise, transforming chaotic AI sprawl into a governed, compliant, and trusted ecosystem. It serves as the essential governance infrastructure layer, providing complete oversight, compliance, and real-time monitoring for every AI system across an organization. Designed for forward-thinking companies scaling AI across diverse models, vendors, and embedded systems, Deeploy eliminates critical blind spots by centralizing control without forcing disruptive migrations or platform changes. Its core value proposition is enabling organizations to accelerate AI innovation and deployment exponentially while simultaneously mitigating risk, ensuring regulatory adherence to frameworks like the EU AI Act, and building immutable trust. By offering flexible onboarding, actionable control frameworks, and predictive monitoring, Deeploy moves governance from a reactive, manual burden to a proactive, automated force multiplier. This allows businesses to harness AI's transformative power with absolute confidence and complete control, turning governance into a strategic accelerator rather than a bottleneck.
About Threat Watch
Threat Watch transcends the conventional realm of cybersecurity tools, embodying a sentient intelligence layer that integrates seamlessly into your digital ecosystem. It represents a transformative leap in cyber defense, converting raw data into a dynamic, living assessment of your organization’s security posture. This platform acts as a centralized cyber health command center, continuously scrutinizing your entire attack surface. From internal assets and software vulnerabilities to external exposures across the clear, deep, and dark web, Threat Watch provides a comprehensive view of your security landscape. By harnessing advanced AI-driven analytics, it delivers real-time, predictive insights that elevate your security strategy from a reactive stance to a proactive and predictive posture. Designed for forward-thinking security teams, IT leaders, and executives, it offers more than mere alerts; it provides a clear, actionable, and prioritized roadmap to cyber resilience. The core strength of Threat Watch lies in its ability to autonomously identify, contextualize, and prioritize risks, empowering you to mitigate threats with unprecedented speed and surgical precision, effectively future-proofing your organization against the ever-evolving digital threat landscape.
Frequently Asked Questions
Deeploy FAQ
How does Deeploy handle existing AI systems without causing disruption?
Deeploy is designed as a non-invasive governance layer. It does not require you to migrate your AI models or change your existing MLOps platforms. Instead, it uses flexible connectors and discovery tools to integrate with your current stack, pulling metadata and establishing oversight without interfering with live systems. This allows you to centralize control and gain visibility without operational downtime or re-engineering costs.
Can Deeploy help us comply with the EU AI Act and other regulations?
Absolutely. Deeploy is built with evolving global regulations like the EU AI Act as a first-class concern. It provides pre-built control frameworks mapped to these standards, guiding you through risk classification, documentation requirements, and monitoring obligations. The platform automates evidence collection and generates audit-ready reports, significantly reducing the manual burden of proving compliance and adapting to new regulatory demands.
What kind of monitoring and alerts does Deeploy provide?
Deeploy offers predictive, real-time monitoring that tracks key performance indicators, data drift, concept drift, and output anomalies for all your AI systems. It provides instant, configurable alerts when metrics deviate from expected baselines or when potential compliance violations are detected. For generative AI, it includes specialized monitoring for output quality, toxicity, and hallucination rates, allowing you to intervene before issues affect users.
Is Deeploy suitable for governing both traditional machine learning and generative AI?
Yes, Deeploy is architected as a universal governance platform for the entire AI spectrum. It provides tailored oversight for traditional ML models, including performance tracking and explainability, and specialized frameworks for generative AI applications, including prompt management, output guardrails, and LLM-specific risk assessments. This unified approach prevents governance silos and provides comprehensive oversight across all AI modalities.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for a wide range of organizations, from small businesses to large enterprises. Any entity that seeks to enhance its cybersecurity posture can leverage this revolutionary tool to protect against evolving threats.
How does Threat Watch ensure data privacy?
Threat Watch adheres to strict data privacy standards and regulations. It employs encryption and data anonymization techniques to protect sensitive information while conducting its analyses, ensuring that your data remains secure.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is built to integrate seamlessly with a variety of existing security tools and systems. This interoperability enhances your current security infrastructure without disrupting workflows.
Is there support available for new users?
Absolutely. Threat Watch offers comprehensive support for new users, including onboarding assistance, tutorials, and a dedicated helpdesk to ensure that your team can maximize the benefits of the platform.
Alternatives
Deeploy Alternatives
Deeploy is the foundational command center for governing and scaling AI, a critical layer of infrastructure for the AI-native enterprise. It transforms chaotic AI sprawl into a governed, compliant, and trusted ecosystem, providing complete oversight and real-time monitoring across all models and vendors. Organizations may explore alternatives for various strategic reasons, such as aligning with specific budget constraints, requiring different feature integrations, or needing a platform tailored to a unique operational stack. The search often stems from a need to balance comprehensive governance with flexible deployment options. When evaluating an alternative, prioritize solutions that offer predictive, automated oversight rather than manual, reactive checks. Look for a platform that serves as a proactive force multiplier, enabling exponential AI innovation while ensuring immutable trust and adherence to evolving regulatory frameworks like the EU AI Act.
Threat Watch Alternatives
Threat Watch is a cutting-edge cybersecurity platform that embodies the next generation of cyber defense through its AI-powered threat intelligence capabilities. As a vital component in the business intelligence category, it serves as a sentient intelligence layer that continuously analyzes and diagnoses your organization's security posture, transforming raw data into actionable insights. However, users often seek alternatives for various reasons, including pricing structures, desired features, or specific platform integrations that may better suit their unique needs. When exploring alternatives, it is essential to consider factors such as comprehensive analytics, real-time insights, the ability to prioritize risks, and overall ease of integration into existing systems. A robust alternative should not only offer a proactive approach to threat management but also ensure that the user experience is intuitive and aligns with your organization's specific cybersecurity objectives.
